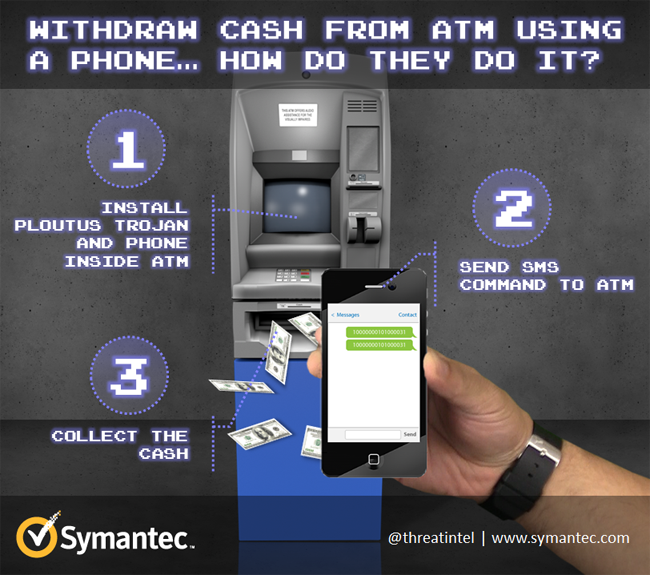
A leading Security Certificate Authority named Symantec has detected a new malware which can steal cash from ATM machines. When Microsoft declared that support for windows XP will cease from April 8, 2014, every bank started to worry about the security of their ATMs. In the world of cyber culprits, hackers are inventing new techniques everyday to steal confidential information and money of companies and internet users. Symantec recently find out an ATM malware named “Backdoor.Ploutus.B” that works on a single SMS pattern in which, attacker sends a simple SMS to compromised ATM and can easily collect the cash. This technique is currently in use by attackers across the world. Below is an image showing that how an attacker withdraw cash from an ATM using a phone.
How Attacker Hack The ATM With Ploutus?
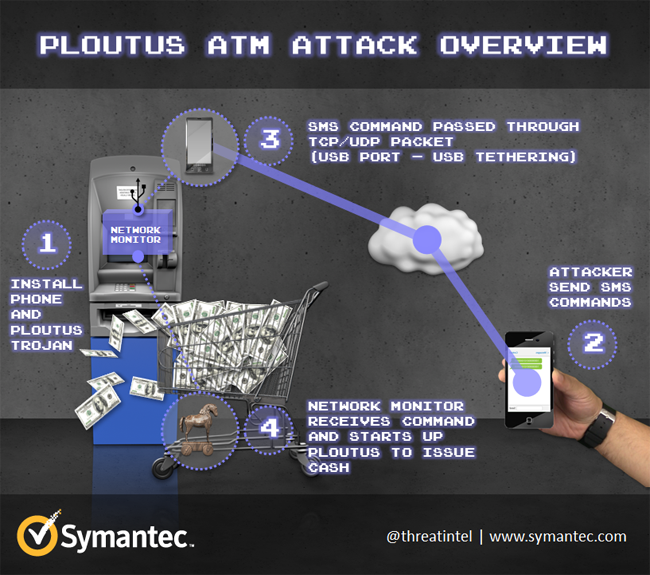
In this type of attack, cyber criminals can remotely control ATM machine with a mobile phone that is connected to the inside of the ATM. A common approach is to use a USB tethering that is a shared connection between a phone and a computer. With the help of USB tethering, attacker connects the Smartphone to the ATM and he can infect ATM with injecting Ploutus malware. Due to USB port, mobile phone also absorbs power from ATM and remains fully charged.
After the completion of set up, attacker sends a command message to the attached inside phone. As soon phone receives the message, it converts the message into a network packet and sends it the ATM through the USB cable. Network packet monitor (NPM) is nothing but a module of malware that works as a packet sniffer and observes all traffic coming to the ATM. As soon, the compromised ATM receives a valid TCP or UDP packet from the phone, the NPM analysis the packet and try to search the already fixed number “5449610000583686” within the packet to carry out the whole data package.
Once the number is identified, the NPM will start to read the next 16 digits and use those numbers to perform a command line to make Ploutus successful. You can see below the command line used in SMS.
cmd.exe /c PLOUTOS.EXE 5449610000583686=2836957412536985
Symantec Security Response team has found many types of malware that targets ATM to steal the money. Out of them, some of malware steal customer’s card information and PIN while other malicious software use in man-in-middle attack.
How To Prevent ATM From Ploutus?
- Symantec Security Response team has given some security measures to prevent such types of malware techniques.
- Upgrade operating system to windows 7 or 8.
- Provide CCTV facility at ATM and provide physical protection.
- Lock down the BIOS to avert unauthorized access like CD ROM, USB stick.
- Use full disk encryption to avert disk tempering.
- Use a system lock down solution like Symantec Data Center Security: Server Advanced product that offers agentless antivirus for virtualized servers.
The above measures can help banks to protect ATM from cyber criminals, and Symantec advised windows XP users to upgrade to Windows 7 or 8.