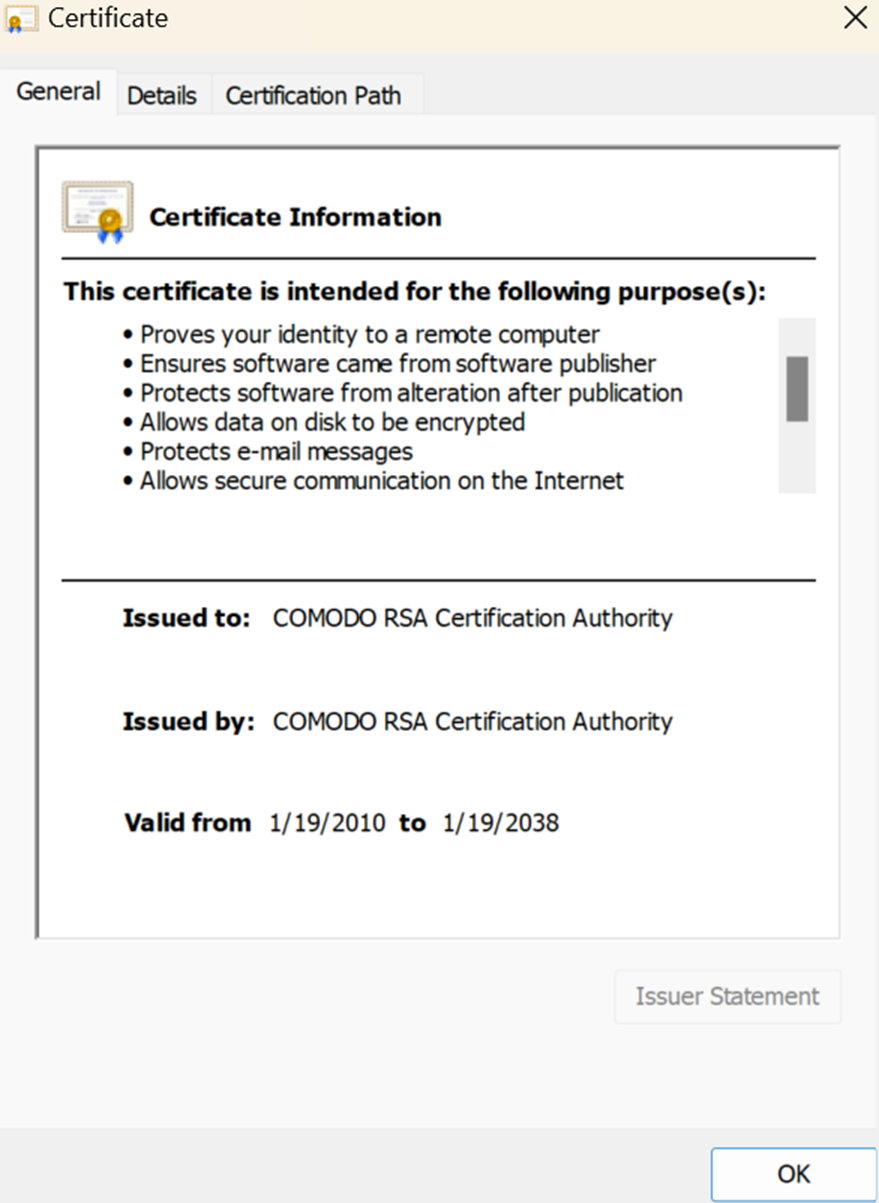
The key difference between root certificates and intermediate certificates is that a root certificate is self-signed, whereas an intermediate certificate is a cross-signed certificate
Cyber-attacks are getting more commonplace than ever. In 2022, there have been several attacks, including the one on microchip giant Nvidia. Attackers gained access to crucial details, employee credentials, and source code for different apps. In addition, it was a ransomware attack where attackers threatened to release more than 1TB of data.
So, how to avoid such attacks on your organization?
Secure Sockets Layers or SSL certificates secure communication and data exchange between two systems. You can use an SSL certificate to keep the data anonymous. Root certificates are the core of any Public Key Infrastructure (PKI) system, which secures your data.
However, PKI systems consist of a certificate chain with root and several intermediate certificates. You need to understand the difference between them for enhanced security of your systems, so here we are with a detailed guide on the difference between root and intermediate SSL certificates. Let’s first understand what is root and intermediate certificates.
What is a Root Certificate?
SSL certificates use encryptions to ensure that your systems are secure, especially from man-in-the-middle attacks. In addition, every SSL-based system has a chain of certificates with a root certificate at its core.
However, the SSL certification process is essential before we understand the chain of certificates. The process begins with private key generation by an organization that wants an SSL certificate. Further, companies need to create a certificate signing request or CSR. Finally, a certificate authority verifies the certificate requestor’s details and issues an SSL certificate.
So, where does root certificate come into play?
Every CA issue certificate based on a chain of trust sourcing back to the root CA. It has multiple certificates in a hierarchical tree structure. Almost browsers and operating systems have root certificate of many CA for higher compatibility.
What is a chain of trust?
A chain of certificates or chain of trust has three significant elements,
- A root certificate acts as the trust anchor for this chain of trust. In broader terms, the root certificate is an authenticator for CA enabling browsers to verify the legitimacy of a website.
- Several intermediate certificates create a security layer between the root certification and server or end-user SSL certificates.
- Server certificates or user certificate is right at the end of the hierarchy, which is the one issued to a specific domain or organization based on validation type.
Most CAs that issue root certificates are operating system developers like Apple, Microsoft, Google, etc. However, it is not restricted to OS developers. Some third-party app developers leverage the system’s certificates or have their code sign certificates by trustworthy CAs.
Every device has a root store, a collection of root certificates with their public keys. So, for example, an Android device will have a root store with all the certificates stored locally on your smartphone.
The root certification process must follow strict guidelines of the CA/B forum, and it should be an X.509 digital certificate. It is also used to issue other certificates in the chain. Other certificates in the chain of trust are intermediate ones, and they are essential for the entire SSL-based system.
What is an Intermediate Certificate?
A PKI system with several root certificate replicates can lead to fraud issues. Apart from the security issues, it is also a management nightmare where you have to manage several trust anchors without linking certificates.
This is where an intermediate certificate comes into play. Root CAs delegate their tasks to intermediate CAs, extending the trust from the anchor to the end server. In other words, such intermediate certificates are a substitute for root certificates.
It creates a layer of security between the server and root certificates, securing their keys from any type of exposure. Differentiating between a root certificate and an intermediate is easy. Just go to the certificate path of your certificate on the system, and you can observe the trust anchor right at the top.
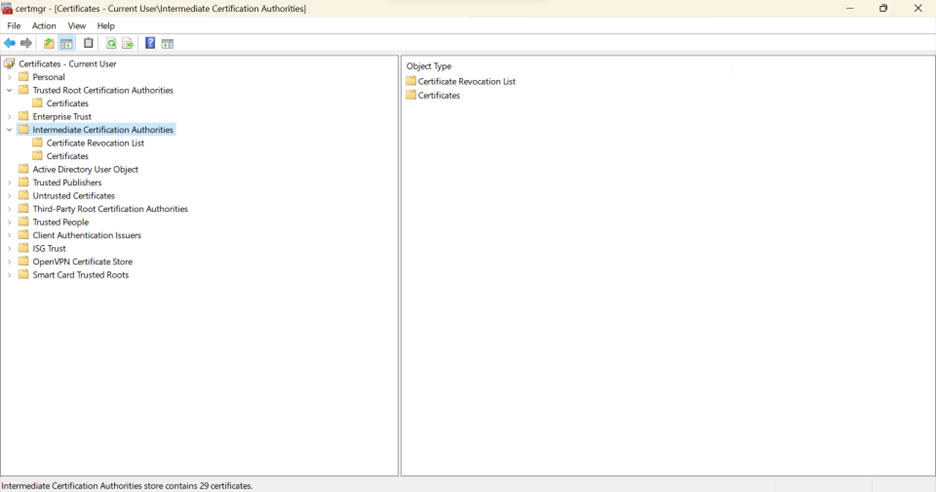
An intermediate certificate is at the bottom, linked to the trust anchor in the certificate path. Further, you can see two distinct directories for root and intermediate certificates in the system’s certificate manager window panel.
However, there are fundamental differences between root certificates and intermediate ones. Let’s discuss them side by side.
Difference Between Root Certificates and Intermediate Certificates
Both root and intermediate certificates are different at their core, functionalities, issuing authority, and more.
| Differentiators | Root Certificate | Intermediate Certificate |
| Core functionality | Root certificates act as a trust anchor in the certificate chain. | Intermediate certificates serve as a link between the root certifications and the server or end-user certificates. |
| Certificate Authority | Root certificates are issued by trusted CAs, also known as the root CA | Intermediate certificates, which internal CAs delegated by Root CAs issue. |
| How are they signed? | Root certificates are high-priority self-signed certificates or signed by highly trustworthy CAs | Root certificate’s private keys help in signing intermediate ones. |
| Validity period | Higher validity than intermediate certificate as long as 20 years in some cases | Lower validity period than root certificates |
| Position in the chain of trust | It is right at the center of hierarchy where every chain of trust leads back to the root certificate | It forms a layer between the root certificate and end SSL certificates. |
Conclusion for Root Certificates vs Intermediate Certificates
Security is the utmost priority for several organizations in the digitally modernized era of business activities. Users access your websites across devices, from smartphones to personal computers and tablets.
So, it becomes vital to have a sound PKI system to ensure advanced security. Knowledge certification chain of trust and root certificate is essential to fine-tune your systems and enable security.
Recommended Reading: