EV code signing certificate carries the highest validation while keeping the private key on Hardware Security Module instead of storing it on the server while standard code signing certificate is vetted with organization validation.
The introduction of malware in an organization’s IT infrastructure can be devastating, and in 2020 alone, over 64% of businesses experienced such breaches. Most of these incidents were caused by malicious apps or private key thefts — that explains why developers must use a code signing certificate and the correct type.
Unfortunately, most developers get confused between standard Code Signing vs EV Code Signing and end up picking the regular one while their project might actually need the EV certificate. After all, there is a thin line of difference between the two, and we’ll discuss that in a while.
Both regular and Extended Validation code signing certificates hallmark the software application’s integrity and security but do so in slightly different ways. Each has its strengths and weaknesses, which one must consider before making a purchase. While the regular one brings a cost-benefit, the extended validation (EV) offers higher validation and trust.
Now that is just the tip of the iceberg, and there are several other differences between EV Code Signing and standard Code Signing. These disparities can make the selection process overwhelming, so we decided to briefly discuss the difference between EV Code Signing and standard Code Signing. This should make the entire process a whole lot easier and less time-consuming for developers and businesses.
What is EV Code Signing Certificate?
The EV code signing certificate is a comprehensive solution for software development firms and other organizations that wish to undergo a more detailed vetting process and get a superior trust seal. It involves a thorough verification of the publisher before the issuance of the certificate.
As this type of certificate is issued to an organization, the keys are stored externally, making it more secure and easy to manage. Now that we have discussed what an Extended Validation code signing certificate is, let us move forward and discuss how the EV code signing works and its key benefits.
How Does EV Code Signing Work?
The EV code signing certificate is a high-end solution designed for mid-sized and large businesses. It begins with an application, which is followed by a detailed verification of the applicant’s business. Once complete, the CA issues one. As it involves detailed verification and requires the applicant to conform to the norms laid down by the CA and the browser forum, its issuance usually takes some time.
Once issued, the applicant can store the private key on the external hardware token and use it to sign the code or the executables throughout the certificate’s validity. The EV code signing process is undeniably far more secure than the standard code signing as it involves using a token on which the private keys are stored. So, the digital signature can only be applied by an individual who has access to the token, which makes it more secure.
This is in stark contrast to how the standard certificate’s keys are stored. Those are stored on the developer’s workstation, which makes them vulnerable to thefts and insider threats. This additional layer of security works exceptionally well for business owners trying to limit access to the private key, which helps prevent its misuse by insiders and external threat actors.
Benefits of EV Code Signing Certificate
The EV code signing certificate offers a plethora of benefits in terms of security and credibility. We shall now discuss some of those now.
#1: Provides Superior Validation
If you are familiar with SSL certificates, you’ll know the difference between organizational and extended validation. The latter requires a more in-depth verification and is rewarded with a much superior trust seal that end-users can see. The same applies to the EV code signing certificate, too and while you are at it, make it a point to get one from a reliable CA.
#2: Prevents Insider Attacks
Unlike the standard code signing certificate, the EV works exceptionally well in keeping a tab on internal security issues because of the token. These internal issues refer to insider threats which 66% of organizations are paranoid about. After all, there has been a 46% spike in insider threats, including intentional and accidental acts by the firm’s employees and associates.
For example, an employee could steal and misuse the private key stored on the workstation, while another may accidentally download an attachment with malware in it. Such attachments can create a backdoor through which the key can be stolen and misused.
This has been witnessed in the Asus case of 2019 when an Asus OS update was packed with malware and digitally signed with the Asus’ private key. That blow was devastating for the tech giant and is something that every app or software developer must learn from. However, you don’t have to worry about it when you use an EV code signing certificate. As the key is stored on a token and not the workstation, its access is limited only to a few responsible individuals.
#3: Protects from External Threats
Over time, the number of cyberattacks launched on businesses has increased considerably, posing a severe threat to all your data, including the private key. If stolen, the private key could be misused to sign code and executables with malicious code in it. This is bound to happen when you store it on the workstation connected to the internet and your IT infrastructure. You can eliminate those risks by using an EV code signing certificate that lets you store the private key on a token and use it to sign executables as and when required.
What is Standard Code Signing Certificate?
The CA issues a standard code signing certificate and allows the developer to digitally sign the code and executables. This type of certificate is issued quickly and does not involve a comprehensive check of the business or its legal existence. Nevertheless, it binds the organization to the code or executable, which serves the purpose for many. In short, it does what it is supposed to do, but nothing beyond that and is therefore ideal for small and midsized development firms.
How Does the Standard Code Signing Work?
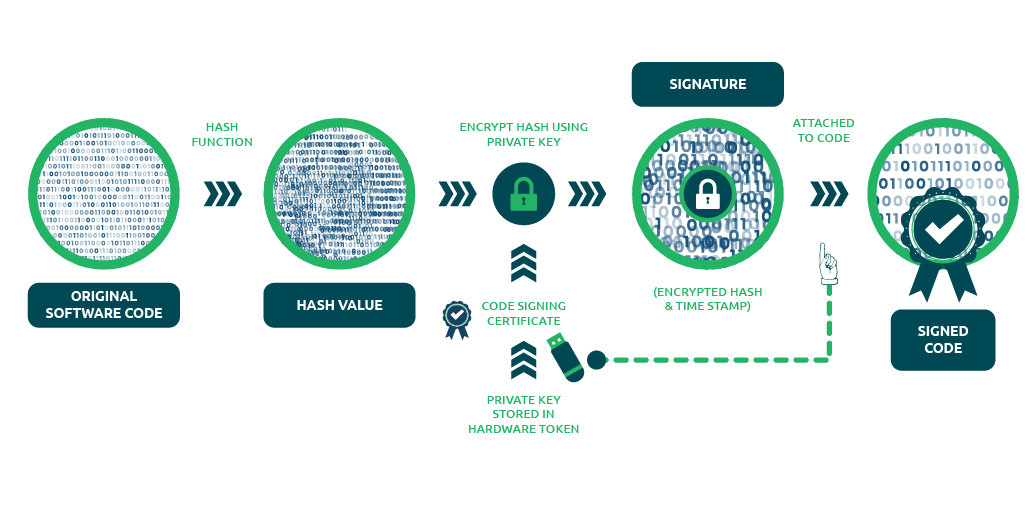
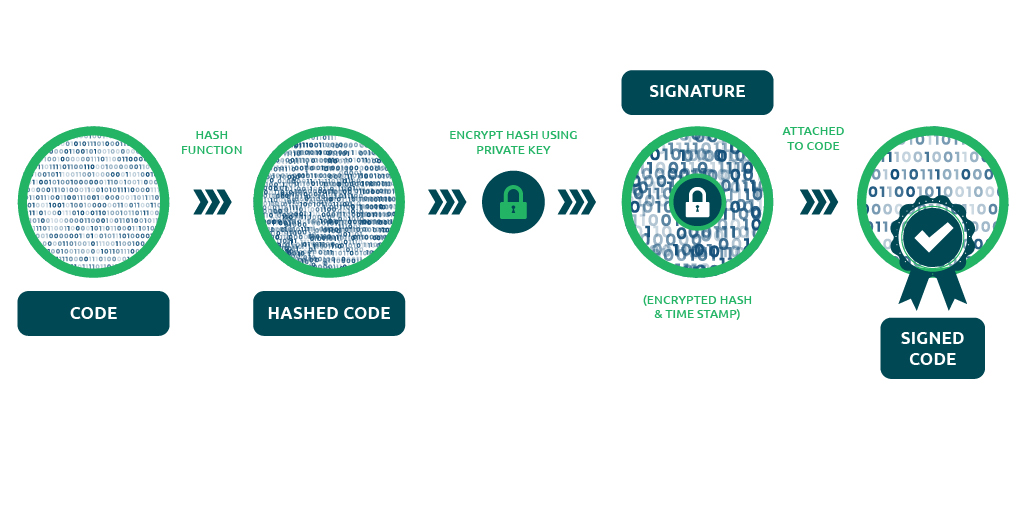
The standard code signing certificate is easy to procure and involves fewer formalities. Upon successful application, it is issued in under 24 hours, and an email link with the private key is emailed to the applicant. This is a string of code that can be stored on the Windows or Mac keychain and then be used to sign the code or the executables. It involves the use of the hash function to confirm the code’s authenticity.
Benefits of Standard Code Signing Certificate
The code Signing certificate is helpful for the authenticity of a code and assures end users that the software is safe to download. Below are some benefits of using a Code Signing Certificate.
#1. Code Integrity:
Code Signing certificate ensures code integrity using a hash function. There are two hashes applied during the process of code signing. One hash is used at the time of signing a code and the other hash should be matched while downloading the software. If both hashes do not match, users will face a security warning during downloading. Also, the timestamp is there at the time of the signing process, which assures that the certificate is still valid in case of certificate is expired.
#2. Publisher’s Reputation:
Code Signing establishes the reputation of a publisher as users can easily identify the name of a verified publisher during downloading. It assures users that the software is from a real publisher/developer and not a fake one. A signed code creates loyalty and trust from users and publishers sides. It removes the issue of tampered with or corrupted software and applications.
#3. Increase in Downloads:
Once trust is established, users would like to purchase and download software/application/driver. Users can easily rely on signed code as they know that the publisher is real and verified. Even, small companies will have a sigh of relief about code authenticity, and they can distribute their software among customers.
#4. Safety for Users:
Users will have a safe experience while using authenticated software code. There will be no security warning or installation failure while downloading software. There will be mutual trust between the software vendors and users and it also helps in an increase in downloads.
#5. Multiple Platforms Compatibility:
The code Signing certificate is compatible with highly reputed platforms including Java, Adobe documents, Windows Phone, Apple OS X software & apps, MS Authenticode, Linux software & apps, Microsoft software & apps (.exe, .dat, .cab, .xpi, .dll, .ocx), Kernel mode software, and MS Office documents. All these platforms recommend signed code for their software and apps. Even browsers also require signed code from trusted CAs and avoid untrusted sources.
EV Code Signing Certificate and Standard Code Signing Certificate – Difference Between
We have discussed how both regular and EV code signing certificates work and although their inherent mechanism involves leveraging the hash function, the storage and the level of validation vary. However, from a cost perspective, standard code signing is a more affordable option. So, while one offers secure storage and superior validation, the other is pocket-friendly and ideal for smaller businesses. Below is a difference between standard code signing and EV code signing.
| Standard Code Signing | EV Code Signing |
|---|---|
| It follows a simple and standard verification process including organization validation. | It offers rigorous validation process followed by the CA/B forum guidelines. |
| The private key is stored on the disk/server. | The private key is stored on an external hardware token for better safety. |
| The issuance time takes up to 3 days. | The issuance time takes up to 5 days. |
| The price is low compared to the EV Code Signing certificate. | The price is high compared to Standard Code Signing certificate |
| It is used to sign earlier drivers before the arrival of Windows 10. | It requires signing Windows 10 kernel mode drivers. |
How to Get EV Code Signing and Standard Code Signing?
| Comodo Code Signing Certificate | Comodo EV Code Signing Certificate | |
| Our Cheapest Price | $226.00/yr. | $296.67/yr. |
| Buy Now | Buy Now | |
| CA Price | $266.00/yr. | $349.00/yr.. |
| Secure | Software & Apps | Software & Apps |
| Validation Type | Organization Validation | Extended Validation |
| Issue Time | 1-3 Days | 1-5 Days |
| USB Token | ||
| Key Encryption | 3072-bit or 4096-bit | 3072-bit or 4096-bit |
| Java Signing | ||
| Microsoft Authenticode Signing | ||
| Apple OS X Signing | ||
| Microsoft Office VBA Signing | ||
| Adobe Air Signing | ||
| Windows Vista X64 Kernel Mode Signing | ||
| Windows Phone Apps Signing | ||
| Qualcomm Brew App Signing | – | – |
| Ms Office Document Security | ||
| Warranty by CA | – | – |
| Refund Policy | 30 days | 30 days |
| Free Reissuance | – | – |
| 24 x 7 Support | ||
| Buy Now | Buy Now |
Recommended Post: