What is Digital Signature and Digital certificate? The question might have popped into your mind when you come across these two names. With the rise in the digital market, digitization is closely linked to all our social and business processes as it improves the efficiency, quality, consistency, and accessibility of processes.
Digital signatures and digital certificates are security solutions that can secure your data from these cyber thieves. Though these words are a bit similar, their synonyms and functions are completely different.
In this short piece of information, we would clarify the difference between a Digital signature and a Digital certificate and make them understand.
What is a Digital Signature, and How does it Work?
Every day thousands of terabytes of digital data are created by organizations all over the globe. Physical documents are being digitized to ensure accuracy and cost benefits as well as vast reachability.
But digital data has one disadvantage, i.e., owner identification. When the data is in digital format, it’s difficult to decide the ownership of the data, and hence it requires a signature in digital format to prove the same. Another issue is that even if the data is digitally signed, verifying the signature’s authenticity is also a tough call.
When a document in a digital format is signed with a digital signature, it can’t be changed or modified. This electronic tool not only verifies whether the data is genuine or not but also assures the recipient of the data/document that a third-party entity does not compromise the data.
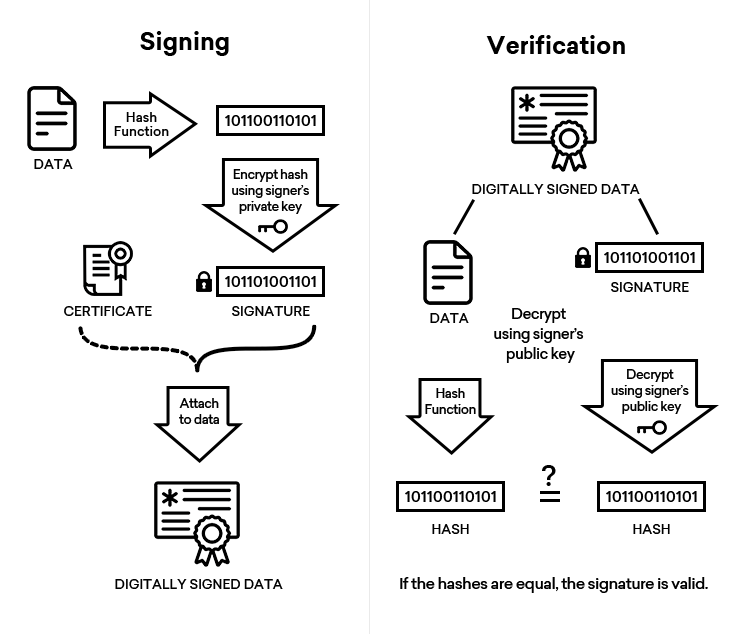
These signatures are just like electronic signatures/prints, which look like coded messages. They use the hashing technique for securing data and a standard format named Public Key Infrastructure (PKI) for global acceptance and robust security.
Working:
Digital signatures avail the Digital Signature Standard (DSS), which can be best explained with the help of an example.
Let’s presume that Alisha wants to send a digitally signed message to Jack. She will need to create a key pair (public and private key) before sending the message. She will then create a message and utilize the private key to encrypt it (hash value). The secured message will be sent to Jack.
She will place the public key in a public location for Jack, who will do two tasks. 1st is to decrypt the message, and the next task is to verify Alisha’s digital signature.
Jack will thus ensure that Alisha sends the message. The hash values for the message will be verified to check their authenticity.
If the hash values match each other, the message is genuine and unaltered, but if the hash values don’t tally, it’s a warning signal stating that the message is compromised.
Why would you use a Digital Signature?
Apart from assuring the originality of the messages and identity verification, some other benefits of a digital signature include:
Authentication: Though the sender’s identity in sending a message is known, the message may seem inaccurate or suspicious. Digital signatures are proofs of authenticity when they are attached to documents, and they are pivotal, especially in the case of financial transactions.
Integrity: Digital messages can be compromised or altered by intruders in the absence of these signatures. Digital signatures safeguard the same, and in case of alteration of messages, the digital signature will become invalid. This cautions the recipient that the message is compromised. In this way, data integrity is assured for both parties.
Accountability: Non-repudiation by the sender is not possible in the case of digital signatures, and this makes them accountable when a message is signed and sent by them.
What is a Digital Certificate, and How does it Work?
Digital certificates or digital identification cards, as you name them, are just like physical ID proofs. These certificates are files that use cryptography and PKI to authenticate the servers, devices, websites, etc.
They are issued by Certificate Authorities (CAs) or reputable government bodies. When the request for a digital certificate is made to the CAs by any person, the CAs verify the requester’s identity and authenticity and all legal documents before issuing the same. The certificate comprises the public key, which is used for digital signatures.
These certificates are pivotal since they verify the identity of the owner before their issuance. When any website or document is secured with a digital certificate, it’s proof that they are genuine and trustworthy since they have passed the vetting process done by the concerned authorities.
Example: SSL (Secure Socket Layer) certificates are digital certificates that secure data with 256-bit robust encryption. These certificates are used in digital communications between the web server and browser.
Benefits:
- It comprises owner information
- It comprises the details of the issuing authority.
- It cannot be compromised or imitated.
- The issuing authority can revoke the certificate in case of emergency (theft).
- The issuing authority can confirm the revocation status.
Working:
When digital certificates do authentication, the organizations are assured about their network being connected with reliable devices. When the signed certificate is issued to an organization, they verify whether the certificate signature with the signature done by the certificate’s private key is matching or not.
Example:
Alice needs to check out the authenticity of Bob’s signed certificate. So, Bob will acquire a digital certificate and register his public key and his details to a CA. The CA, after verification, will issue the certificate (signed by private key), which has Bob’s public key and other details.
Alice will later check the digital certificate, the public key, and the signature. Alice will also tally the hash values with the ones mentioned in the certificate. When they match, the certificate is valid.
The use of a Digital Certificate to Sign Documents:
When a signer signs the digital document, the concerned parties have faith in the digital signature since they trust the verification process done by the CA during the time of issuance.
In short, a digital certificate ties a digital signature to a concerned entity, and these signatures guarantee that the original data is not altered.
Both these digital securities are used for authentication, but digital signatures differ from digital certificates because digital certificates are used to authenticate persons. In contrast, digital signatures are used for data authentication.
Digital Signatures vs Digital Certificates – What You Should Know
The difference between a digital signature and a digital certificate can be judged from the below-mentioned factors.
#1. Basic Function:
- Digital signatures confirm the integrity of data and verify the authenticity of the document.
- Digital certificates verify the owner’s identity and enhance site trustworthiness.
#2. Process:
- The document on which the digital signature is done is encrypted by the sender and decrypted by the receiver, respectively. The same is done with the help of asymmetric keys.
- In the case of digital certificates, the reliable Certificate Authority carries the entire procedure of verification, key generation, and issuance once the request for the same is received.
#3. Motto:
- Digital Signatures assure document authentication, data integrity, and non-repudiation.
- Digital certificates assure authentication, data confidentiality, and data integrity apart from site security.
#4. Issuance:
- Digital signatures are issued to specific individuals by authorized agencies.
- CAs issue digital certificates after verification of owner identity and business.
#5. Ensure:
- These signatures ensure that the signer can’t repudiate the document on which they have signed.
- These certificates ensure that the client and the browser communication stays secured with encryption.
#6. Work On:
- The working of Digital signatures is based on Digital Signature Standard (DSS).
- The working of digital certificates is based on cryptographic keys and encryption securities.
#7. Use of Security:
- For security purposes, digital signatures use the hashing function.
- For security purposes, digital certificates use cryptographic keys.
#8. Main Purpose:
- The main purpose of digital signatures is to prevent the forging of documents and statements.
- The main purpose of digital certificates is to provide a secured communication channel for online transactions and to gain trust.
#9. Visibility:
- These signatures are attached to documents and show authenticity.
- These certificates are installed on websites and show the owner’s identity.
#10. Task:
- The main task of digital signatures is to verify that the document transferred between the sender and the receiver is not altered.
- The main task of digital certificates is to enhance trust between the customer and the site owner.
#11. Creation:
- The creation of digital signatures is made using SHA-1 or SHA-2 algorithms.
- The creation of digital certificates is done in the X.509 format.
#12. Encryption:
- In the case of digital signatures, if message encryption is required RSA algorithm is used.
- In the case of digital certificates, messages are encrypted using SHA-2 encryption, and only the receiver can decrypt the same.
#13. Signed & Verified:
- Signature on digital signatures is done using the signer’s private key, and the signer’s public key verifies the same.
- Digital certificates are issued by CA, which are verified by the end-user.
#14. Validation:
- Digital signatures validate the data sent.
- Digital certificates validate the sender’s identity.
Conclusion
Digital signatures and digital certificates are essential since one identifies the owner of the document, whereas one identifies the organization’s identity respectively.
Digital signatures are electronic tools that are just like physical signatures, but they validate document authenticity. Certificate Authorities issue digital certificates after proper verification are available in multiple validations (Domain Validation, Organization Validation, Extended Validation). They secure site domains and sub-domains, and they are installed on the server and secure the data with encryption.
It does not matter whether SHA-1/SHA-2 algorithms are used or RSA is used; both these certificates’ tasks are commendable in the digital market.
The digital market needs such security solutions for preventing cyber-attacks and hacker intrusions.